Effectively protect your applications from attacks
With SysEleven DDoS Guard, you get comprehensive protection against DDoS attacks and ensure that your applications stay accessible at all times.
Stay secure with SysEleven DDoS Guard
We offer a comprehensive and scalable solution that proactively monitors your infrastructure and neutralizes threats in real time before they can do harm. Powerful components and the expertise of our cloud and network teams provide you with all-around protection.
Comprehensive protection
Safeguard your infrastructure against DDoS attacks – whether volumetric, protocol-based, or application-layer attacks – before they reach your infrastructure.
Real-time monitoring
Continuously monitor your networks up to OSI Layer 4 and receive instant notifications of suspicious activities – which lets you react quickly.
Scalability
Scale protection as needed to fend off even the largest attacks without compromising the performance of your applications.
Our peering partners





Technical features at a glance
Automatic engineering for DDoS traffic
FlowSpec mitigation / traffic washing
L3/L4 anomaly dectection and mitigation
Geofiltering on request
Manual mitigation for previously unknown attack vectors
Access to the mitigation portal
Selective blackholing
Reporting & alarms
SysEleven DDoS Guard
We’ve compiled the key information about SysEleven DDoS Guard in a factsheet.

Filter protection
SysEleven DDoS Guard gives you comprehensive protection for your network and enables targeted threat mitigation. With upstream filtering up to Layer 4, harmful data packets are filtered out early, well before they reach your network.
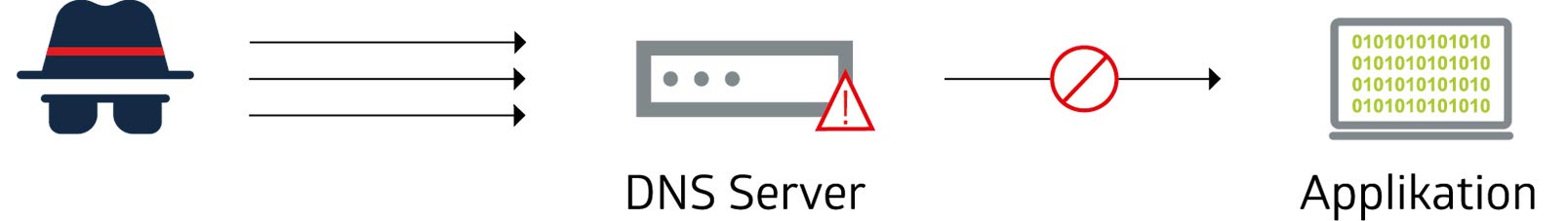
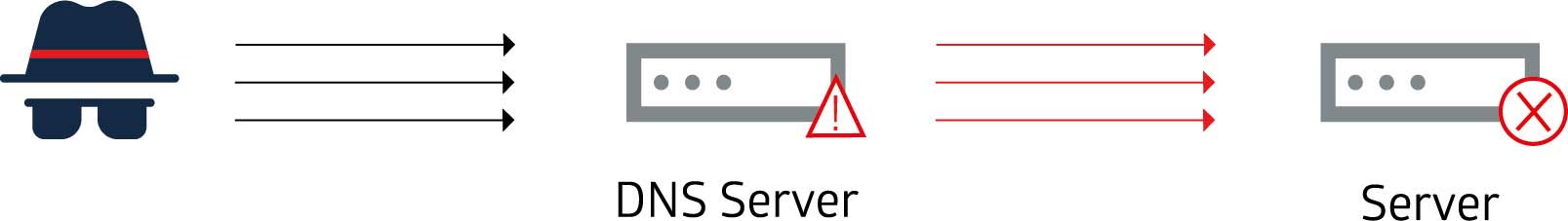
DNS floods
DNS flood attacks disrupt DNS resolution. This leads to reduced performance or even unavailability of your website, API, or application.
UDP floods
Attackers exploit the functions of open DNS or NTP resolvers to overwhelm a target server or network. They do this with amplified request traffic where the payload is larger than the original request.
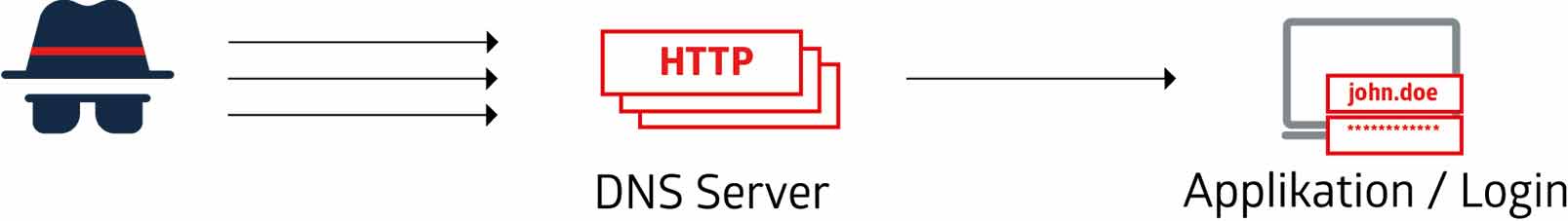
HTTP floods
HTTP flood attacks generate large volumes of HTTP, GET, or POST requests from various sources.the application layer and degrade service or reduce availability.
Use cases

When critical infrastructure (KRITIS) fails or is disrupted, this can impact public life or the safety and health of the general public. DDoS attacks could disrupt essential services significantly. Therefore we place the highest priority on protecting this infrastructure to ensure security of supply.

Large online retailers use DDoS protection to safeguard their websites during major sales events like Black Friday. SysEleven DDoS Guard distinguishes between legitimate customer requests and malicious traffic. This lets the company handle high traffic spikes while avoiding outages or delays.

For SaaS providers, DDoS protection is essential to make sure that their services stay available constantly and customers stay satisfied. The consequences of a DDoS attack can range from loss of revenue to penalties for failing to meet SLAs – even losing customer trust.
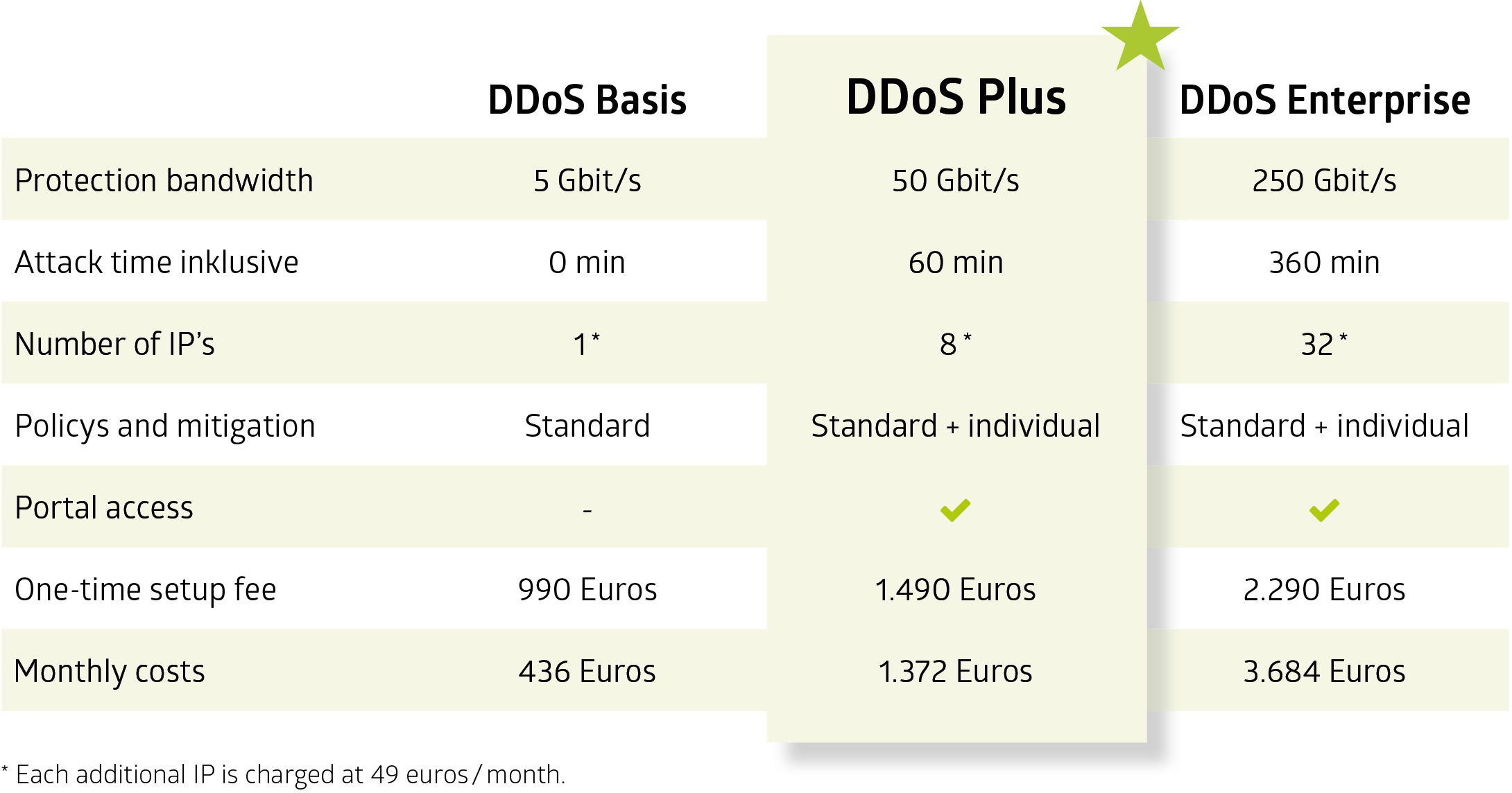
Pricing
SysEleven offers three different packages with varying mitigation capabilities against DDoS attacks.
FAQs
Customers who have subscribed to the Plus package can opt to automatically upgrade to the Enterprise package until the end of the contract if the Plus package’s bandwidth is not enough during an attack. Traffic can also be blocked without pre-authorization until an authorized Enterprise package order is received. SysEleven implements traffic filters at the entry points of traffic into our networks. This is why the total mitigated attack volume is higher than the guaranteed performance in the packages.
SysEleven DDoS Guard is designed to provide the best conditions to anticipate and mitigate DDoS attacks inexpensively and quickly. We strongly recommend that you not wait until an attack occurs. However, limited ad-hoc deployment is available at increased costs, though it may offer a different level of protection than a well-planned defense. Additionally, we can only guarantee the bandwidth of filtered traffic up to the level of capacity you initially ordered.
Get in touch with us
Are you interested in our DDoS Guard? Please get in touch with us.
We’ll take a look at the requirements for your software project together.
If you wish to submit a form via HubSpot forms, we require your consent to load this service. You can revoke your consent at any time with future effect via “Edit cookies” in the footer.
Further information
